The New Frontier of Chip Observation
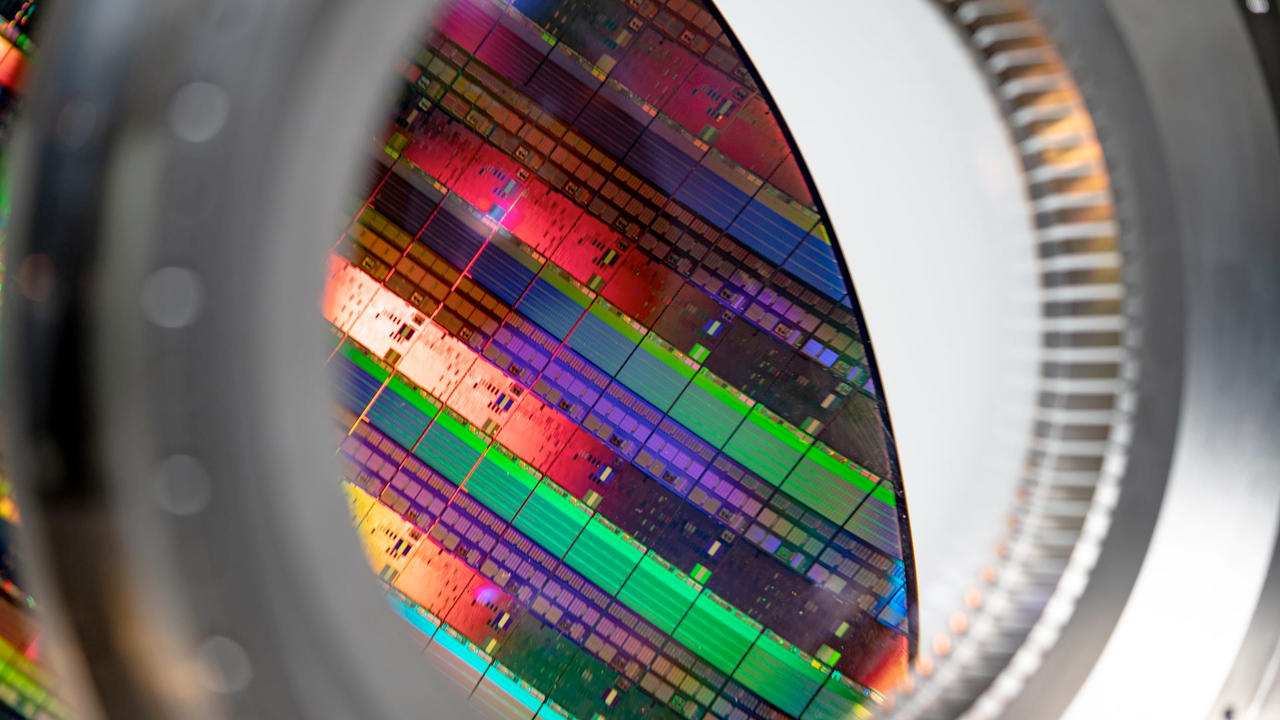
The world of microelectronics is in constant evolution, pushing the limits of miniaturization and chip complexity. In this scenario, a new technology emerges that promises to revolutionize the understanding of a CPU's internal workings. This innovation allows for "seeing" a processor's transistors in action, offering an unprecedented window into the most intimate operational mechanisms of silicio. The ability to monitor activity at the transistor level could have profound implications for both advanced diagnostics and cybersecurity.
ASML, a recognized leader in semiconductor manufacturing equipment, is often at the center of discussions about the industry's most advanced technologies. Although the source does not specify its exact role in this discovery, the mention of ASML suggests a context of cutting-edge research and development in lithography and chip analysis, where the ability to inspect silicio with such granularity is fundamental for improving production processes and the quality of final products.
Terahertz Radiation: A Double-Edged Sword for Security
At the core of this technology is the use of terahertz radiation. These electromagnetic waves, which fall in the spectrum between microwaves and infrared, possess unique properties that make them ideal for penetrating non-conductive materials and revealing structural and dynamic details at a microscopic level. In the context of chips, terahertz radiation can interact with the electric and magnetic fields generated by active transistors, allowing their activity to be mapped in real-time.
However, this observational capability carries a significant potential threat: data theft. If it is possible to "see" transistors in action, it is theoretically possible to decipher activity patterns corresponding to the processing of sensitive data. This scenario opens the door to new forms of side-channel attacks, where information is not stolen through software vulnerabilities, but through the physical analysis of the chip's emissions or responses during its normal operation. The possibility of extracting data while a chip is running represents an unprecedented challenge for hardware security.
Implications for Data Sovereignty and On-Premise Deployments
The prospect of terahertz radiation-based attacks has direct repercussions for organizations prioritizing data sovereignty and on-premise deployments. For CTOs, DevOps leads, and infrastructure architects, the physical and logical security of hardware is a fundamental pillar. If an attacker could physically access a server and use this technology to spy on CPUs, data protection guarantees, even in air-gapped environments, could be compromised.
This scenario adds another layer of complexity to the evaluation of TCO and the risks associated with self-hosted infrastructures. The choice to keep AI/LLM workloads on-premise is often motivated by the need for total control over data and hardware. However, if silicio-level vulnerabilities emerge, it is imperative that security strategies evolve to include countermeasures against these advanced threats. For those evaluating on-premise deployments, AI-RADAR offers analytical frameworks on /llm-onpremise to assess the trade-offs between security, performance, and costs, also considering emerging risk scenarios like this one.
The Future of Hardware Security
The discovery of this observational capability and the potential risk of data theft via terahertz radiation underscore the importance of continuous research in hardware security. Chip manufacturers will need to explore new architectures and shielding techniques to mitigate these threats. This could include the development of materials more opaque to terahertz radiation, the implementation of active countermeasures at the silicio level, or the adoption of internal signal obfuscation techniques.
The battle for data security is moving ever deeper, from software to hardware, down to the transistor level. For companies managing sensitive data and critical artificial intelligence models, staying updated on these emerging threats and adapting their security strategies will be crucial to maintaining the integrity and confidentiality of their operations. Collaboration among researchers, chip manufacturers, and security experts will be essential to address these challenges and ensure a more secure digital future.








💬 Comments (0)
🔒 Log in or register to comment on articles.
No comments yet. Be the first to comment!