Portafogli Hardware Falsi: Un Rischio Concreto per la Sicurezza Digitale
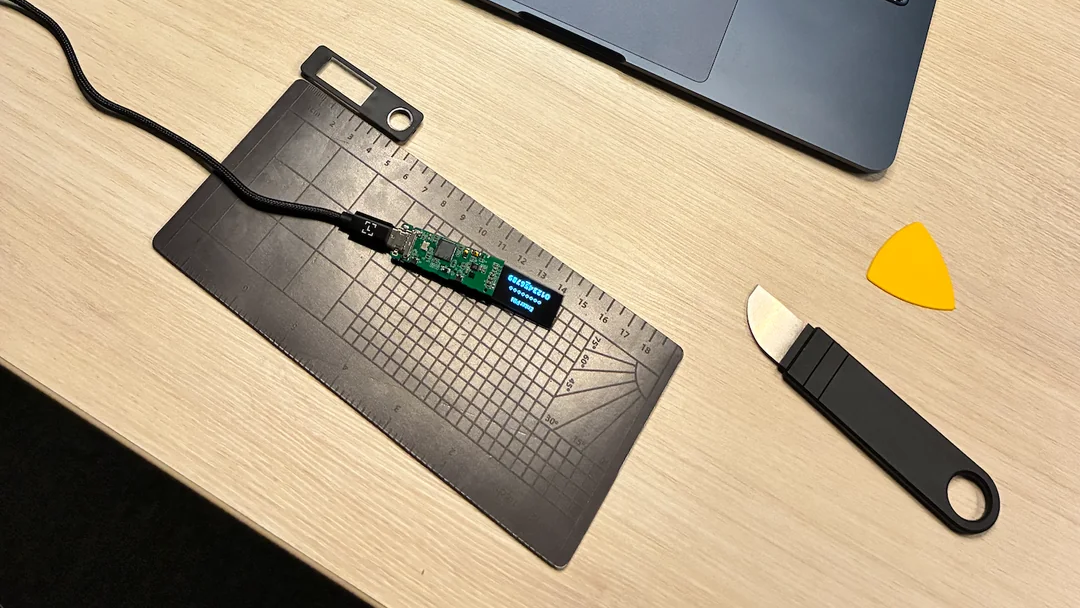
L'integrità dell'hardware rappresenta un pilastro fondamentale per la sicurezza di qualsiasi infrastruttura digitale, specialmente in contesti dove la sovranità dei dati e il controllo sono prioritari. Un recente episodio ha messo in luce una minaccia tangibile: l'acquisto di un portafoglio hardware Ledger Nano S+ contraffatto. Questo dispositivo, un clone estremamente convincente dell'originale, ha quasi ingannato un utente esperto, esponendolo a un tentativo di phishing.
L'incidente evidenzia come la sofisticazione delle contraffazioni possa rendere difficile, anche per gli addetti ai lavori, distinguere un prodotto autentico da uno fraudolento. La capacità di un clone di replicare fedelmente l'aspetto e la sensazione di un dispositivo originale crea un falso senso di sicurezza, aprendo la porta a vulnerabilità critiche che potrebbero compromettere asset digitali e informazioni sensibili. Per utenti meno esperti, il rischio di cadere vittime di tali truffe sarebbe stato ancora più elevato.
Il Rischio del Controverso Hardware nella Supply Chain
Il caso del portafoglio hardware falso non è un evento isolato, ma un campanello d'allarme sulla vulnerabilità della supply chain tecnicica. La proliferazione di hardware contraffatto introduce rischi sistemici che vanno oltre il singolo utente o dispositivo. Ogni componente non autentico, sia esso un portafoglio hardware, una GPU, un modulo di memoria o un chip di rete, può contenere backdoor, firmware malevolo o difetti progettuali che compromettono la sicurezza e l'affidabilità dell'intera infrastruttura.
Per le organizzazioni che implementano soluzioni AI/LLM on-premise, la fiducia nell'hardware è non negoziabile. La garanzia che ogni elemento dello stack tecnicico sia autentico e privo di alterazioni è essenziale per mantenere la conformità normativa, proteggere la proprietà intellettuale e assicurare la resilienza operativa. Un singolo punto di debolezza nella catena di fornitura può minare anni di investimenti in sicurezza e compliance, rendendo vani gli sforzi per costruire ambienti air-gapped o altamente protetti.
Implicazioni per i Deployment On-Premise e la Sovranità dei Dati
Il focus di AI-RADAR sulla sovranità dei dati e sui deployment on-premise rende questo tipo di minacce particolarmente rilevante. Quando si sceglie di mantenere i carichi di lavoro AI/LLM all'interno dei propri data center, la responsabilità della sicurezza ricade interamente sull'organizzazione. Questo include la verifica dell'autenticità di ogni pezzo di hardware, dal server alle schede grafiche, fino ai dispositivi di sicurezza come i portafogli hardware per la gestione delle chiavi crittografiche o l'accesso a sistemi critici.
La presenza di hardware contraffatto può avere conseguenze devastanti, dalla perdita di dati sensibili all'esposizione a attacchi informatici mirati, fino alla compromissione dell'intera rete. Per i CTO, i DevOps lead e gli architetti di infrastruttura, è imperativo implementare processi rigorosi di procurement e verifica. Questo include l'acquisto da fornitori autorizzati, l'ispezione fisica dei dispositivi e, quando possibile, l'utilizzo di strumenti di verifica crittografica per confermare l'autenticità del firmware e del software preinstallato. La minimizzazione del TCO non deve mai compromettere la sicurezza fondamentale dell'hardware.
Strategie di Mitigazione e Vigilanza Costante
Per mitigare i rischi associati all'hardware contraffatto, le organizzazioni devono adottare un approccio proattivo. Acquistare hardware solo da canali ufficiali e rivenditori autorizzati è il primo e più importante passo. È fondamentale diffidare di offerte che sembrano troppo vantaggiose per essere vere, poiché spesso nascondono prodotti non autentici o compromessi. Inoltre, è consigliabile implementare procedure di controllo qualità e verifica all'arrivo della merce, che possono includere l'esame di sigilli di sicurezza, numeri di serie e packaging.
La consapevolezza e la formazione del personale sono altrettanto cruciali. Gli utenti devono essere istruiti sui segnali di allarme che possono indicare un prodotto contraffatto e sulle migliori pratiche per la gestione della sicurezza digitale. In un panorama tecnicico in continua evoluzione, dove le minacce diventano sempre più sofisticate, la vigilanza costante e un'attenta due diligence sull'integrità dell'hardware sono indispensabili per proteggere gli asset digitali e garantire la sovranità dei dati. Per chi valuta deployment on-premise, AI-RADAR offre framework analitici su /llm-onpremise per valutare trade-off e rischi legati all'infrastruttura.










💬 Commenti (0)
🔒 Accedi o registrati per commentare gli articoli.
Nessun commento ancora. Sii il primo a commentare!