The Canvas Attack and the Scale of the Breach
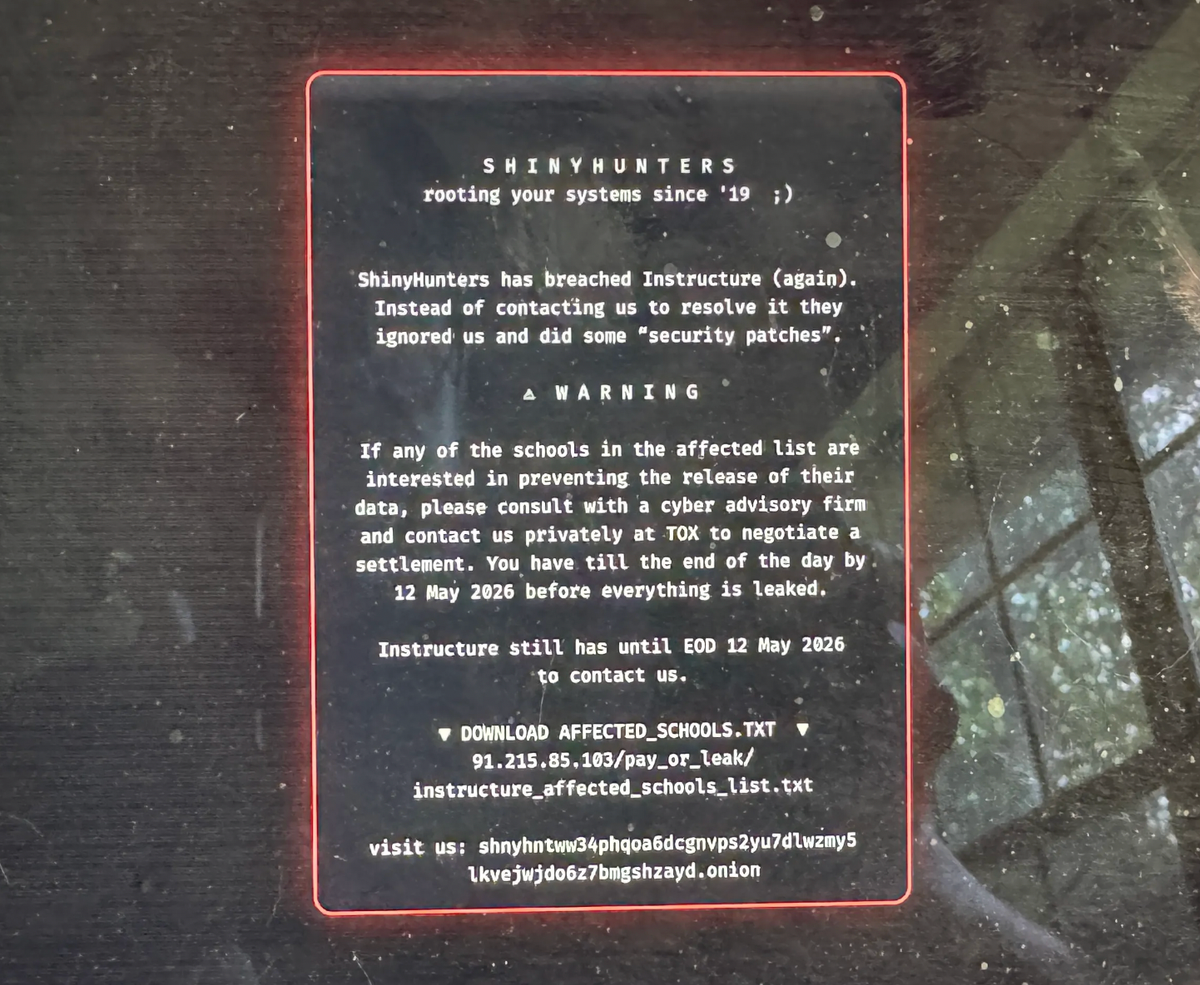
On Thursday afternoon, millions of students across thousands of universities and K-12 schools found themselves locked out of Canvas, the educational technology software that has become the de facto core of many classes. The ShinyHunters ransomware group hacked Canvas's parent company, Instructure, and reportedly stole "billions" of messages, accessing data from over 275 million individuals, according to the hackers themselves. The attack also locked students out of the platform.
Later, Instructure was able to mostly bring Canvas back online, although it is unclear whether the company paid a ransom. The incident revealed the inherent vulnerability in centralizing the educational and personal data of millions of students in a single service. Canvas acts as a portal where teachers post assignments and lectures, host discussion boards, and students can message each other and their teachers, as well as connect with other educational technology software. Instructure confirmed that the stolen data includes names, email addresses, student ID numbers, and messages among Canvas users, also revealing that it was breached twice, once on April 29 and again on the Thursday of the main incident.
The Vulnerability of Centralization and the Role of Self-Hosted Solutions
Ian Linkletter, a digital librarian specializing in emerging education technology with twenty years of experience in the sector, called the Canvas hack "the biggest student data privacy disaster in history." His perspective is particularly relevant, having previously exposed privacy concerns in remote test proctoring software like Proctorio, and having faced a lawsuit that was later dropped. Linkletter emphasizes how the scale and sensitive nature of the stolen information make this incident unprecedented.
The expert highlighted how, about ten years ago, there was a rapid shift from self-hosted learning management system (LMS) applications, often hosted on local servers with greater data control, to a centralized model based on cloud services from U.S. tech companies. This transition led to "total faith" in a single vendor, concentrating all data in one place. According to Linkletter, the widespread nature of the attack across all Canvas customers suggests that Instructure had access to a quantity of data not strictly necessary, making the breach so pervasive and unprecedented in its scope.
Implications and Risks for Sensitive Data Privacy
The leakage of message content is particularly concerning, as it facilitates the creation of highly customized phishing attacks. An attacker could leverage pre-existing conversations to deceive victims, making the attacks far more effective. Furthermore, messages between students and teachers often contain extremely sensitive information. Linkletter recalled how students communicate delicate personal circumstances to instructors, such as family bereavements, medical conditions, disability accommodation needs, disputes, or even sexual assault allegations. The dissemination of such information to hundreds of millions of people can cause significant and lasting harm.
For organizations evaluating the deployment of critical systems, the Canvas incident offers a warning about the trade-offs between the convenience of centralized cloud services and the need to maintain sovereignty and control over their data. AI-RADAR, for example, offers analytical frameworks on /llm-onpremise to evaluate the cost, security, and compliance implications of self-hosted versus cloud-based solutions, especially for AI/LLM workloads that require particular attention to privacy and security.
The Institutional Response and the Lesson for the Future
Linkletter's primary concern, as the situation unfolds, relates to the response of educational institutions. The expert believes that students should have been warned days earlier, and that only the second breach, which made the problem evident to everyone, prompted schools to react. The delay in informing students increases stress, chaos, and the potential risk to their privacy and safety. Timeliness and transparency in communication are crucial to mitigate damage and allow individuals to take protective measures.
This incident underscores the importance for organizations to carefully evaluate deployment architectures, prioritizing, where possible, self-hosted or hybrid solutions that ensure greater control over data location and security. Data sovereignty, regulatory compliance, and the ability to operate in air-gapped environments become decisive factors in mitigating risks such as those that emerged with the Canvas breach. The lesson is clear: excessive centralization, if not accompanied by robust security measures and a clear risk management strategy, can turn into a single point of vulnerability with catastrophic consequences.
💬 Comments (0)
🔒 Log in or register to comment on articles.
No comments yet. Be the first to comment!