Introduction: The New Frontier of Infrastructure Security
China recently announced the successful test of an electro-hydrostatic actuator designed to operate in deep-sea environments. This device, capable of cutting undersea cables up to 3,500 meters deep, represents a significant technological advancement and, according to state declarations, suggests potential deployment readiness. While the news focuses on an engineering innovation, its implications extend far beyond the maritime domain, touching the core of global digital infrastructure security and resilience.
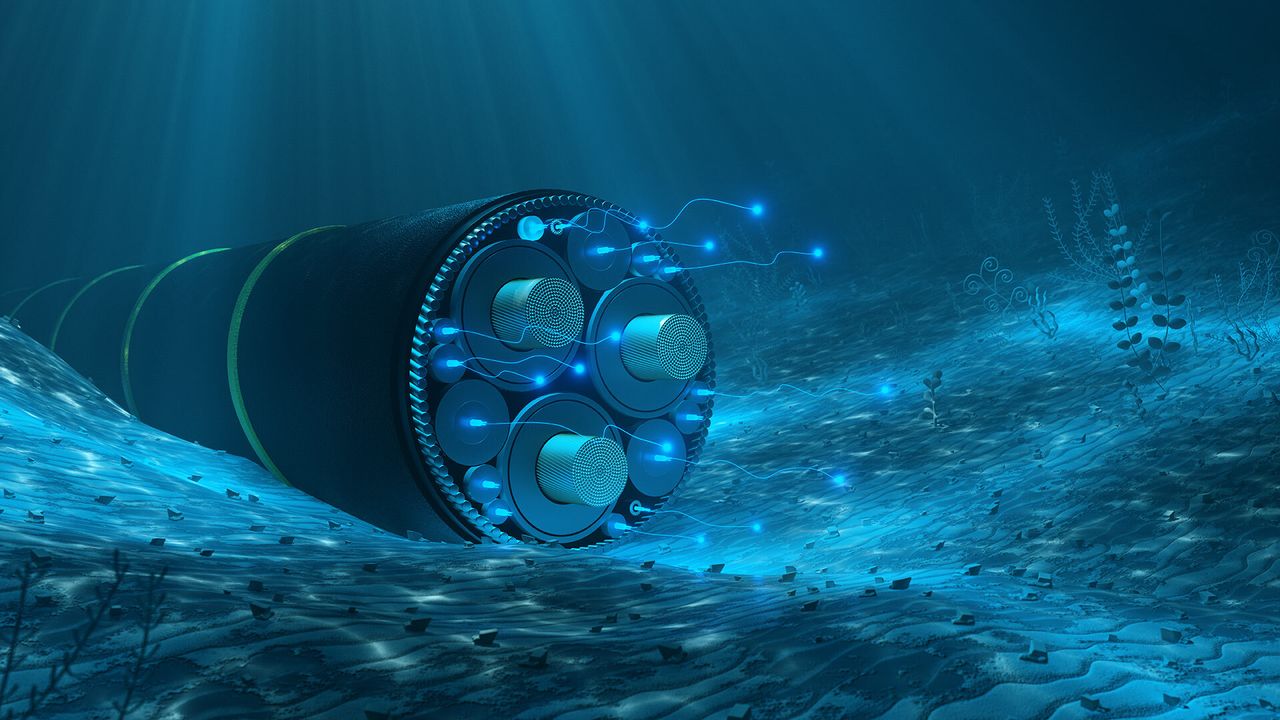
Undersea cables form the backbone of worldwide internet connectivity, carrying the vast majority of international data traffic. Their integrity is fundamental for the functioning of the digital economy, communications, and ultimately, for the data sovereignty of nations and businesses. A device with the capability to compromise these digital arteries introduces a new level of complexity in assessing infrastructural risks.
The Digital Backbone and its Strategic Vulnerabilities
The global network of undersea cables is a complex and vital infrastructure, essential for data transfer between continents. These cables, often as thick as a garden hose and composed of protected optical fibers, are vulnerable to a variety of threats. Historically, damage has primarily been caused by natural events like earthquakes or accidental human activities, such as ship anchoring or trawling. However, the ability of a specialized actuator to operate at great depths introduces a strategic and deliberate dimension to these vulnerabilities.
The possibility of targeted disruptions to data traffic raises significant concerns for the operational continuity of any digital service, including artificial intelligence workloads. The reliance on uninterrupted connectivity for accessing cloud resources, synchronizing distributed data, or executing remote Inference processes makes every disruption a potential critical point of failure. Organizations must therefore consider not only the robustness of their internal systems but also the resilience of the external network infrastructure upon which they depend.
Implications for Data Sovereignty and On-Premise Deployment
The vulnerability of global network infrastructures has direct implications for data sovereignty and deployment strategies. For companies and institutions managing sensitive or critical data, the ability to ensure that data remains within specific geographical boundaries and under their control is a top priority. Undersea cable disruptions could compromise the ability to access or transfer data across borders, complicating compliance management and information protection.
In this context, on-premise or hybrid deployment solutions gain even greater strategic importance. Keeping Large Language Models (LLM) and their associated computing stacks within controlled data centers, or in air-gapped environments, reduces dependence on external connectivity for critical operations. This approach offers greater control over the physical and logical security of data, latency, and Throughput, as well as mitigating risks associated with potential global network disruptions. The evaluation of TCO for such infrastructures must now also include the implicit cost of resilience and data sovereignty.
Resilience and Future Strategies for AI Infrastructure
The news of the Chinese test serves as a warning for organizations operating with AI workloads that rely on robust global connectivity. It is imperative to develop resilience strategies that go beyond simple internal redundancy. This includes diversifying network paths, considering satellite backup solutions (albeit with trade-offs in terms of latency and bandwidth), and, most importantly, a thorough evaluation of the benefits of self-hosted deployment for the most critical operations.
For those evaluating on-premise deployment, AI-RADAR offers analytical frameworks on /llm-onpremise to understand the trade-offs between costs, performance, security, and data sovereignty. The capability of an undersea actuator to compromise global connectivity underscores the importance of an infrastructural architecture that can ensure operational continuity and data protection, even in the face of unforeseen geopolitical or infrastructural risk scenarios. Resilience is no longer just a technical issue but a fundamental component of business strategy.











💬 Comments (0)
🔒 Log in or register to comment on articles.
No comments yet. Be the first to comment!